You can have the best venue, the best speakers, the best run of show…
…and still break your event program with one simple mistake:
permission chaos.
It usually starts innocently.
One event turns into a program. One team turns into five. And suddenly you’ve got 15–50 people touching the same event setup:
marketing, updating pages and emails
Ops managing check-in and onsite workflows
speakers uploading content
sponsors asking for last-minute changes
agencies building assets
vendors supporting production
temp staff scanning badges on event day
And the pressure is always the same: “Just give them access. We’re behind.”
That’s how it happens.
When you don’t have role-based access control (RBAC) in place, the same problems repeat across every event:
Everyone is an admin: Because it’s faster in the moment. Until someone changes a setting they didn’t understand and your registration flow breaks.
Shared logins: Because it feels convenient. Until you need to figure out who edited the page, who exported the attendee list, or who sent the wrong email.
Accidental edits: A vendor tweaks a template. A contractor updates a form field. A regional team changes a setting thinking it’s local. Now the whole event behaves differently.
Data exposure: Someone who only needs check-in access can see attendee data or dashboards they should never touch.
Last-minute lockouts: The day before launch, the wrong people have access, and the right people don’t. Now you’re firefighting instead of leading.
This is exactly why event teams need RBAC, not as a “security best practice,” but as a way to keep your program operational.
Role-based access control is what lets you move fast without losing control.
Instead of giving access person-by-person, you define:
the roles your team actually uses (marketing, ops, onsite staff, speakers, agency partner)
The permissions each role needs to do the job
And you keep everything scoped so work happens safely
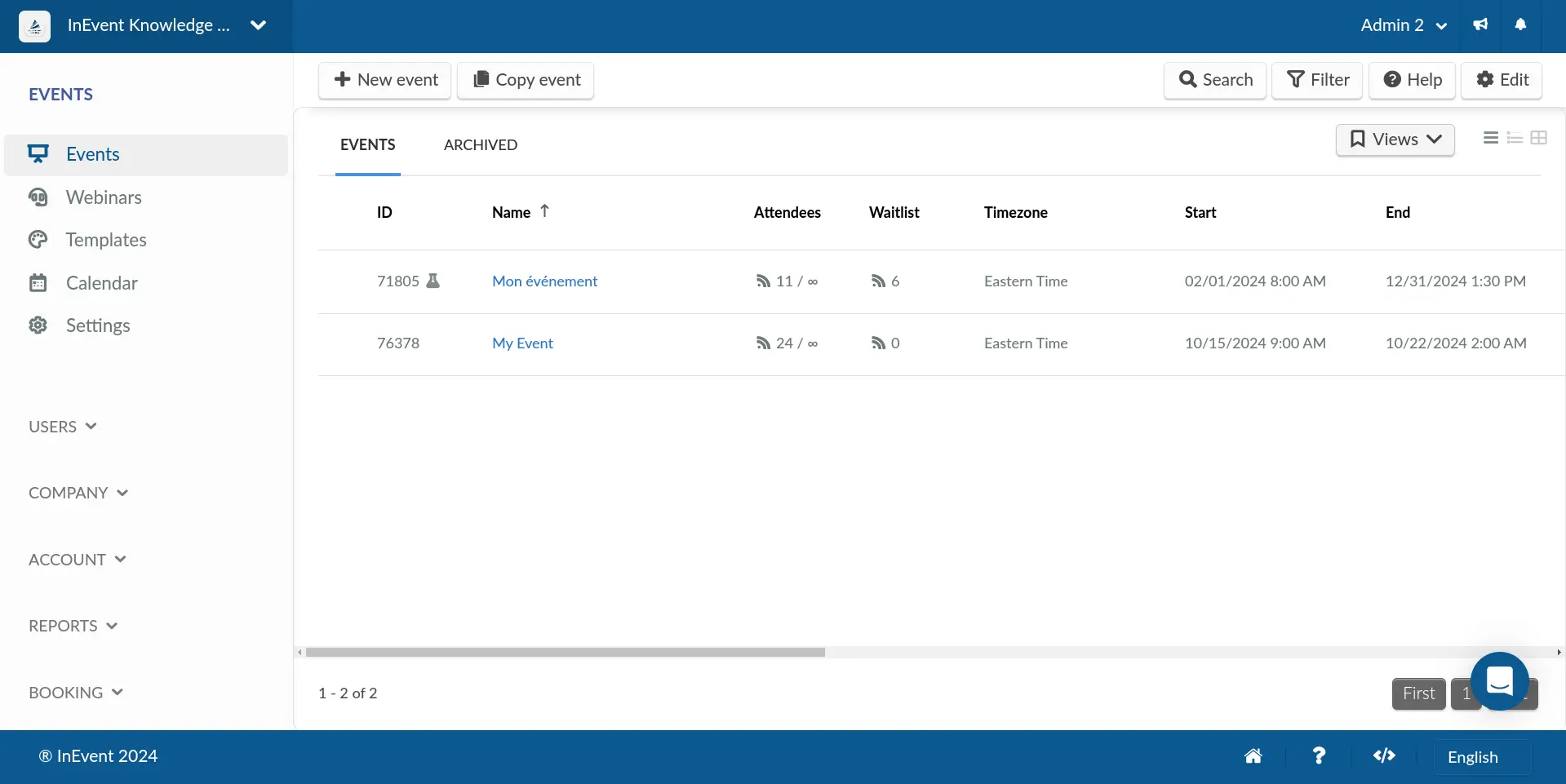
InEvent supports structured role levels and permission management concepts like standard permission levels (Admin, Staff, Speaker, Data Collector, and more), which help event teams separate responsibilities without slowing down execution.
And here’s the truth: if you run enterprise events or multi-event programs, RBAC isn’t optional. It’s one of the first things that determines whether your platform feels enterprise-ready or held together.
Next, we’ll define RBAC and show how it applies to the real workflows that event teams run every day.
Role-based access control (RBAC) is a way to manage access by assigning permissions to roles, then assigning users to those roles. That keeps access consistent, repeatable, and scalable as your team grows.
In other words, you don’t decide access on a person-by-person basis. You decide it by job function.
That matters in event software because events are never run by “one person.” They’re run by a moving team.
To keep RBAC simple, remember this:
Role = who they are (their job)
Permission = what they can do
Examples of roles in an event program:
Marketing manager
Ops lead
Data collector (check-in/scanning staff)
Speaker
Agency partner
Examples of permissions in event software:
Edit registration fields
Update the event website
Send email communications
Manage agenda/session settings
Scan attendees at check-in
View dashboards and reports
Export attendee data
So instead of saying, “What can John do?” You say, “What should an Ops Lead be allowed to do across events?”
That’s how you prevent permission creep while keeping the team moving.
A lot of software can survive messy access control for a while.
Events can’t.
Because events are high-speed environments with constant collaboration:
changes happen daily (sometimes hourly)
multiple teams touch the same build
deadlines are unforgiving
Temporary access is also normal in events:
contractors
venue staff
agencies
production partners
temp onsite staff
And when RBAC isn’t in place, mistakes become public and expensive:
wrong page goes live
wrong email gets sent
registration data breaks reporting
attendee data is exposed to the wrong person
check-in staff can’t access what they need on event morning
RBAC reduces these risks by enforcing the principle of least privilege: people only get the access they need to do their job, not everything “just in case.”
Next, we’ll clear up a common confusion that trips teams up: RBAC vs “roles and permissions” vs permission profiles and how this shows up in real event workflows (especially when agencies and regional teams are involved).
Event teams hear these terms thrown around a lot, especially during platform evaluations. They sound similar, but they’re not the same thing. And if you don’t separate them, you end up building a permission model that looks fine on paper… then breaks the moment an agency, regional team, or contractor joins the project.
Here’s the simplest way to think about it.
RBAC is the system behind clean access control.
Roles are the wrapper: They represent job functions like Marketing Manager, Ops Lead, Onsite Staff, Speaker.
Permissions are the building blocks: They represent actions like “edit registration,” “send emails,” “scan attendees,” “view reports.”
RBAC means you assign users to roles, not permissions user-by-user. Because user-by-user access is how things get inconsistent, messy, and impossible to audit later.
This is the difference between “we gave people access” and “we have a permission model.”
With RBAC, you’re building something repeatable. That’s what makes it scalable.
In practice, most event teams need RBAC with flexibility. Because event teams aren’t always clean-cut.
Sometimes you need roles like:
“Agency partner (website only)”
“Regional marketer (registration + email, no global settings)”
“Ops contractor (check-in only)”
“Speaker manager (speaker assets only)”
That’s where permission profiles come in.
InEvent permission profiles are designed to let you create customized access at either:
the company level (for multiple events), or
the event level (for one specific event)
This is practical RBAC: you define a profile once, then assign it to the right people instead of rebuilding access rules every time.
And InEvent positions this as administrative, customized access through permission profiles.
Here’s the sweet spot for event programs:
Standard roles cover the common needs: Admin, staff, speaker, data collector… the roles you use on almost every event.
InEvent documents standard permission levels like Admin, Staff, Speaker, Data Collector, Translator, and User, which makes it easier to create consistent defaults.
Custom profiles handle edge cases: Agencies, regional teams, client teams, special workflows, and “this person needs access to only one thing.”
That’s where permission profiles and bundles stop you from giving someone admin “just to get the work done.”
The result is what enterprise teams care about most: speed without chaos, and governance that doesn’t slow the program down.
RBAC is useful for every event team. But some teams hit the wall faster than others.
If any of these descriptions sound like your world, RBAC isn’t a nice-to-have. It’s how you keep the program running without constant rework.
Field marketing programs move fast:
quick builds
frequent events
changing cities
rotating support staff
You don’t have time for permission drama.
But field marketing has one major risk: over-permissioning.
Because when you’re launching a dinner next week and someone needs access today, the temptation is always:
“Just give them admin.”
RBAC fixes that by creating role-based access patterns you can reuse. Your onsite scanner gets scanner access. Your marketer gets comms access. Your agency gets page access. Nobody gets the keys to the building.
Enterprise event teams live in the world of governance:
brand standards
legal review
IT requirements
procurement checks
security questionnaires
And procurement always asks some version of:
“Who has access, and how is it controlled?”
RBAC gives you an answer that doesn’t sound like chaos.
It shows you’re running a program with discipline, where access is role-based and controlled, not improvised.
InEvent supports permission profiles and customized access at company or event level, which helps enterprise teams structure access cleanly across portfolios. (faq.inevent.com)
Agencies and production partners need access to execute.
But they rarely need access to everything.
They may need to:
update website sections
upload assets
adjust the agenda
support production workflows
They usually should not have by default:
broad attendee exports
access to unrelated events
full control over security settings and integrations
RBAC is what lets you collaborate with partners without exposing client/attendee data or risking accidental changes outside their scope.
This is one of the clearest use cases for permission profiles in InEvent: external partners can manage specific areas without full access. (faq.inevent.com)
Internal events bring a different kind of sensitivity:
leadership updates
training programs
employee lists
internal-only materials
These programs also repeat, which means you need a setup you can reuse safely:
the same roles every month
the same access boundaries
predictable workflows for moderators and staff
RBAC creates secure access patterns you can repeat without rebuilding permissions from scratch.
A lot of RBAC guidance is written for IT teams managing internal systems.
Event programs are different.
You’re managing fast launches, rotating staff, outside partners, and high-stakes deadlines. So the RBAC principles that work best for event software are the ones that keep your team moving and keep governance clean.
Here are the five that actually hold up in real event operations.
If your default role is “Admin,” you don’t have RBAC. You have hope.
Least privilege means:
people get only what they need to do their job
not everything they might need “just in case”
Why this matters in events:
most mistakes aren’t malicious, they’re accidental
admins can break workflows without realizing it (registration fields, emails, core settings)
temp staff and contractors come and go
RBAC best practice supports least privilege because it reduces risk and improves governance, especially in systems with many users.
A practical event rule:
Start small. Add access only when there’s a clear reason.
This is the principle that saves multi-event programs.
Because the biggest RBAC failure in event platforms happens when:
someone helps on one event
and suddenly they can access every event
Portfolio safety means you separate:
platform-level governance roles (company level)
event-level execution roles (event level)
InEvent documents this structure as “company and event levels,” which is designed to support separation and control across event portfolios.
This separation protects you from:
accidental edits on the wrong event
sensitive internal events being visible to the wrong users
agencies seeing unrelated client events
RBAC only becomes powerful when it’s repeatable.
If every event has its own unique set of roles, you’re rebuilding governance from scratch each time.
Standardize roles like:
Program Lead / Admin
Marketing Manager
Ops Lead
Onsite Staff / Data Collector
Speaker
Agency Partner (limited)
Then use those same roles across your entire program:
onboarding becomes simple
teams know their lane
event launches speed up
fewer mistakes creep in
InEvent supports standard permission levels (including roles like Admin, Staff, Speaker, and Data Collector), which helps teams build consistent defaults.
External partners are essential, but “forever access” is a slow leak.
Events use outside help all the time:
agencies for pages and content
vendors for production support
contractors for operational help
So you need a simple operational habit:
Access should expire when the work ends.
Time-bound access does two things:
reduces long-term data exposure risk
prevents permission sprawl across multiple events
This is also where customized access matters: partners can manage specific areas without needing full control. InEvent’s permission profile approach is designed for this kind of external collaboration without full access.
If your onboarding process is “give them admin and fix it later,” you’ll always be fixing it later.
A clean RBAC process looks like this:
assign a role or permission profile when someone joins
scope it to the right event(s)
remove access when the work ends
review access regularly (especially before major events)
It’s not about being strict. It’s about reducing last-minute chaos.
Because nothing feels worse than realizing, the day before launch, that:
your onsite staff can’t access check-in
your agency can access the wrong event
or your reporting is exposed to people who don’t need it
This is one of the most important RBAC concepts for event teams. It’s also where many programs get stuck, because they treat access as one big bucket.
It’s not.
InEvent breaks access into company and event levels, which helps teams control governance and execution separately.
Here’s what that means:
Company-level access is the “platform governance” layer.
It’s for the people who need to manage how your organization uses the platform across multiple events.
Who should have company-level access:
platform owners
core admins
governance leads (event tech lead, ops governance, sometimes IT/security)
This matters because multi-event programs need consistency:
standardized roles and permission profiles
controlled onboarding/offboarding
clean governance across regions and departments
Without company-level governance, every event becomes its own one-off system, and your portfolio gets harder to control every quarter.
Event-level access is “execution for this one event.”
It’s for the people doing the day-to-day work inside a specific event.
Who should have event-level access:
event owners
producers
regional marketers
onsite staff (scoped access)
speakers (limited access)
agencies (scoped access to areas/events)
It's safer for operational teams because operational teams usually don’t need platform-wide access to do their jobs.
They need access to:
the event they’re building
the workflows they’re running
the sections they’re responsible for
Event-level access keeps them fast without exposing everything else.
Here’s the enterprise reassurance you need your platform to support:
“Access to one event does not mean access to all events.” That separation matters because it prevents:
accidental edits across the wrong event
agencies or vendors seeing unrelated events
data exposure across internal and external programs
permission sprawl across your portfolio
And when procurement or IT asks, “How do you control access across events?” you have a clean answer that isn’t based on trust or manual effort.
RBAC sounds like a “framework,” but in a real event program, you need a workflow you can actually follow.
Here’s the practical way to run role-based access control in InEvent without slowing your team down. Think: set the defaults, build the profiles, speed it up with bundles, and only get fancy when you need to.
InEvent’s event environment includes common permission levels such as:
Admin
Staff
Speaker
Data Collector
Translator
User
These give you a clean baseline for your most common roles, so you’re not reinventing access rules from scratch.
When to use each (high-level):
Admin - Use for: program owners and event owners responsible for governance and configuration.
This person should be accountable for standards, approvals, and overall setup.
Staff - Use for: internal team members who manage parts of the event (marketing, ops, support) without needing full platform governance.
Speaker - Use for: presenters who need access to speaker tasks (session details, uploads where enabled), not event configuration.
Data Collector - Use for: operational roles like check-in/scanning and onsite data capture. This is the role that keeps lines moving.
Translator - Use for: translation support workflows (where applicable).
User - Use for: basic access where someone needs limited interaction, not control.
Check-in staff shouldn’t see dashboards. They need to operate check-in and scanning. They don’t need broader access to reporting or configuration.
This role mapping is one of the biggest wins of RBAC in event software: the right people can do the work without holding the keys to the entire event.
Standard permission levels are the baseline.
Permission profiles are where RBAC becomes usable in the real world.
Because real teams aren’t just “Admin vs Staff.”
You need roles like:
“Marketing manager (website + registration + comms)”
“Ops lead (check-in + onsite workflows)”
“Agency partner (website sections only)”
“Vendor (onsite support only)”
InEvent’s documentation describes permission profiles and customized access, including creating profiles at:
Company level (useful when you want consistent access setups across multiple events)
Event level (useful when one event needs a unique setup)
Why teams use this: So external agencies and partners can manage specific areas without full access. This is one of the most common RBAC pain points in event programs, and permission profiles are the clean way to solve it.
RBAC falls apart when it takes too long to implement.
That’s why bundles matter.
In plain terms: Permission bundles are pre-grouped permissions for specific operations or areas.
Instead of toggling a long list of individual permissions, you assign a bundle that matches the job.
Why this matters:
faster onboarding
fewer mistakes
more consistent access across the portfolio
less “just give them admin” pressure
InEvent publishes a List of permission bundles, which helps teams understand how permissions are grouped.
Not every event needs attendee permission levels, but when you do, it matters.
Common cases:
VIP attendees
sponsors/exhibitors
restricted groups (internal-only sessions, private roundtables)
special access tiers
InEvent documents permission levels for attendees, which supports these scenarios where attendee access needs to be structured beyond “everyone sees everything.”
This is the section you’ll come back to during every event build.
Because the biggest RBAC win is not theory. It’s having a default setup you can reuse without thinking.
Use these as your “standard role set” for event programs.
Full access + governance responsibility
Give this role full access because they’re accountable for:
standards
approvals
program-level consistency
reporting structure
permission governance
This role should not be the person doing every small task. Their job is to keep the system clean and protect the program.
Website + registration + comms (no system/security by default)
Give this role access to:
website content updates
registration workflows and fields (within standards)
email templates and comms flows
agenda content collaboration
Keep them out of:
security settings
system-level configurations
broad exports unless needed
This lets marketing move fast without accidentally breaking governance.
Check-in + scanning + onsite workflows + session tools
Give this role access to:
check-in and scanning setup
session scanning / attendance workflows
operational views needed to run onsite execution
Keep them out of:
unrestricted registration edits
full email controls
global account settings
Ops should be able to run the event without being able to rewrite the system.
Minimal access: check-in + scanning only
This role should have:
check-in/scanning access only
the minimum attendee data needed to do the job
They should not have:
dashboards and reporting
attendee exports
website access
registration editing
admin settings
This is your least-privilege role. It’s also one of the most important for reducing real-world risk on event day.
(Reference point: Data Collector in InEvent’s permission levels.)
Upload content, view schedule, limited tasks
Give speakers access to:
their session details
content uploads (where enabled)
speaker profile tasks
Do not give access to:
registration
attendee data
agenda-wide editing
reporting
(Reference point: Speaker in InEvent’s permission levels.)
Scoped access, time-bound, exports only if necessary
Agencies typically need access to:
website sections and content
agenda/session updates
asset uploads
specific build tasks
They typically should not have:
attendee exports
integration/security settings
global account settings
access to unrelated events
Two rules that keep you safe:
Scope access to what they’re doing (areas), not everything.
Scope access to the event(s) they support, not the entire portfolio.
Event separation matters because one client/event should not expose another. InEvent’s company and event levels support the idea that access to one event doesn’t automatically grant access to all.
(And this is exactly why teams use permission profiles: partners can manage specific areas without full access.)
If you’re evaluating event software, RBAC can sound like a box to tick.
Don’t treat it that way.
Because when access control is weak, you feel it fast:
slower launches
more mistakes
messy agency collaboration
harder approvals
higher risk with attendee data
Use this checklist to spot the difference between “basic roles” and real RBAC that scales for event programs.
This is portfolio safety.
You should be able to give someone access to one event without giving them access to all events.
InEvent documents company and event levels as separate layers for structured governance.
What to look for: clear separation, not “everyone on the account sees everything.”
Standard roles cover the basics (admin, staff, speaker, onsite scanner).
Custom permission profiles handle real life:
agencies that need website access only
regional teams that need comms but not system settings
vendors that need operational access only
InEvent supports customized permission profiles at company or event level. And it positions permission profiles as granular administrative access (enterprise-friendly).
RBAC fails when implementation is too slow.
Permission bundles (pre-grouped permissions) help you onboard faster and reduce mistakes because you’re not toggling individual access settings every time.
InEvent provides a documented list of permission bundles.
This is a make-or-break question for enterprise programs and agencies.
Agencies often need access to:
pages, content, agenda updates, assets
They usually should not have by default:
exports
integrations
global settings
access to unrelated events
InEvent’s permission profiles are explicitly positioned as a way to give external partners access to specific areas without full control.
This is where many teams over-permission.
Onsite staff should be able to:
check people in
scan badges/tickets
keep lines moving
They should not need:
dashboards
exports
build settings
comms controls
InEvent documents roles like Data Collector, which aligns closely to check-in/scanning and operational data capture.
Not all attendees are the same.
Some events need differentiated access for:
VIPs
sponsors/exhibitors
restricted groups
private sessions
InEvent documents permission levels for attendees to support these scenarios.
If a platform can’t answer these clearly, you’ll end up managing access manually, slowing down launches, and increasing risk as your event program grows.
If you’re running more events with more people involved, you already know the pattern:
More users. More partners. More last-minute requests.
And suddenly you’re not managing an event anymore. You’re managing risk.
Because when access isn’t controlled:
the wrong person edits the wrong setting
agencies see more than they should
temp staff get more access than they need
reporting breaks because someone changed fields midstream
approvals slow down because IT and procurement don’t trust the setup
You don’t need stricter people. You need a cleaner system.
InEvent supports role-based access through standard permission levels and permission profiles that can be created at the company level or event level, so you can keep governance tight across a portfolio.
We’ll map your real team structure (field marketing, ops, agencies, internal stakeholders) to:
roles and standard permission levels
permission profiles for customized access
clean company vs event separation
So your team can move fast without losing control.
Book a personalized demoRBAC (role-based access control) in event software is a system where you assign permissions to roles (like marketing, ops, onsite staff, speakers), then assign users to those roles, so access stays consistent and scalable across events.
Roles are the job functions you want to standardize (Marketing Manager, Ops Lead, Onsite Staff).
Permission profiles are the reusable permission setups you build to match those roles (including customized profiles for edge cases like agencies or regional teams). InEvent supports permission profiles and customized access at company or event level.
Company-level access is for platform governance across multiple events (admins, program owners, governance leads).
Event-level access is for people working inside one specific event (event owners, producers, regional marketers, agencies scoped to that event). InEvent documents this separation as company and event levels.
Onsite staff should have the minimum access required to operate check-in and scanning, without broader access to dashboards, exports, or event build settings. InEvent’s permission levels include operational roles like Data Collector, which aligns with scanning and onsite data capture workflows.
Give agencies access based on scope:
limit access to the event(s) they’re supporting
restrict them to the areas they need (pages/content/agenda)
avoid exports unless required and approved
remove access when the engagement ends
InEvent permission profiles are designed for giving partners access to specific areas without full access.



